Application Gateway with Public facing Web Apps
The most common use of Application Gateway is to expose web sites running on VM’s. I’m going to walkthrough configuring an existing App Gateway to target a Web App running on the public Azure App Service, and then securing the Web App to only take traffic from the Application Gateway. By putting an Application Gateway in front of your website, you can make use of the Web Application Firewall that it provides.
Lets start with creating the Web App. I’m using a standard ASP.NET web forms app from Visual Studio, and have tweaked the main page to output all of the HTTP headers onto the default web page so i can see what’s going on. Here’s the code needed to do that.
foreach (var headerKey in Request.Headers.AllKeys)
{
string headerVal = Request.Headers.GetValues(headerKey)[0];
lblHeaders.Text += headerKey + " : " + headerVal + "<br />";
}
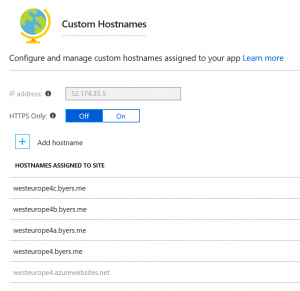
Once i’ve published it to Azure Web Apps, i now need to add my custom domains. This is pretty easy – with your Domain Registrar, you add a CNAME entry for the right subdomain to point to the FQDN for your web app. EG. WestEurope4.byers.me maps to WestEurope4.azurewebsites.net.
After you’ve done this for all the subdomains you want, you come back to the Azure Portal, Verify each domain and Add each hostname in the Custom Domains section of your Web App.
At this point we’re ready to configure/create the Application Gateway. You can find several scripts here; https://github.com/Gordonby/Snippets/tree/master/Powershell/AppGatewayForPublicWebApps
I can recommend the CreateAppGW-ForWebApp-v2 script because it creates the AppGW. This means that it rules out any config mistakes/issues you may have on an existing gateway. However there is a script there for when you have an existing gateway which i’ve used a couple of times.
NOTE: If you’re using a script that creates the Application Gateway, it will take over 30 minutes to provision.
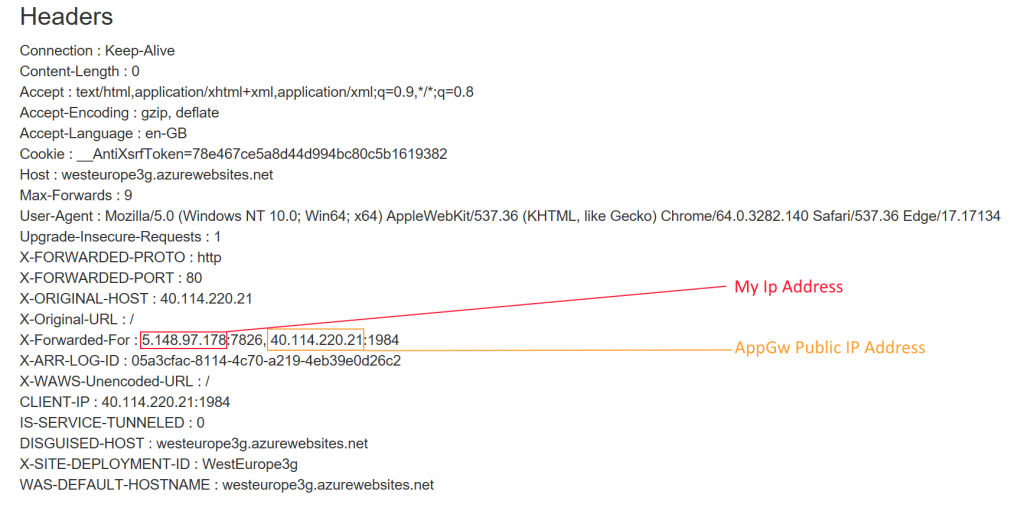
After the Application Gateway has been created, you can now flip the DNS CNAME(s) to target the Application Gateway instead of the Web App directly. You should use the cloudapp.net address associated with the Application Gateways IP address. For me, this is f7a6e9e7-be60-4c41-b5a5-d211f5f56a91.cloudapp.net.
Once you have made the DNS changes, and they have been acknowledged by the various DNS servers and your cache you’ll get a page that looks like this.
This just leaves the process to lockdown the Web Application to only take traffic once it’s originated from the Application Gateway.
Azure App Service Static IP Restrictions
https://docs.microsoft.com/en-us/azure/app-service/app-service-ip-restrictions
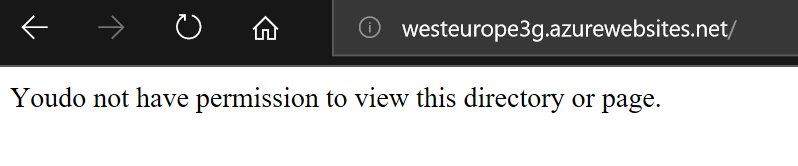
After configuring the IP restriction with the IP address of your Application Gateway, when navigating to your Web App directly, you will be told;
This just leaves one remaining gotcha. Application Gateway only supports Dynamic Public IP Addresses. This of course means that should your Application Gateway change IP (not an expected operation, but still possible) you will need to adjust the configuration of your Web App IP Restriction.
New-AzureRmApplicationGateway : FrontendIpConfiguration /providers/Microsoft.N
etwork/applicationGateways/AppGwForWebAppsStatic/frontendIPConfigurations/fipcon
fig01 of Application Gateway with SKU tier WAF can only reference a
PublicIPAddress with IpAllocationMethod as Dynamic.
Application Gateway will support a Static IP address soon, but as of the time of writing – there is only a private preview programme open for it. https://docs.microsoft.com/en-us/azure/application-gateway/create-zone-redundant