Microsoft Graph vs AAD Graph with PowerShell example
About the Microsoft Graph
The Microsoft Graph API has been around for a while now. It lets you interact with a plethora of different Microsoft services, in a very consistent manner. Utilising the Graph API through MSAL is quite common, but there’s less examples of accessing it through other scripting languages - even PowerShell! There is however an active GitHub project for a PowerShell SDK, but in many cases the examples in the documentation are missing. Additionally, there aren’t many real world examples (blogs etc) of people leveraging the module.
Many mature users of the Microsoft Graph tend to query the API directly with HTTP commands, but I shall not yield :)
The AzureAd Module
The official AzureAd PowerShell module is a notable mention here. If you look at the Connect-AzureAd documentation, you’ll see it takes a MsAccessToken (for the Microsoft Graph). However (at the point of writing) all of the cmdlets i use don’t use that token, instead they all need the AadAccessToken. Indeed, the Azure PowerShell modules and the AZ CLI both use the Azure AD Graph API rather than the Microsoft Graph. I’m sure this will change over time, but as Microsoft are advising migration to Microsoft Graph - it does feel like a bit of a minefield at the moment.
Scripts Compared
Given the example of something i’ve worked on a lot recently… Managing Service Principal Application secrets, here’s how the PowerShell compare. Both examples start from the perspective of already having obtained an Access Token.
Microsoft Graph
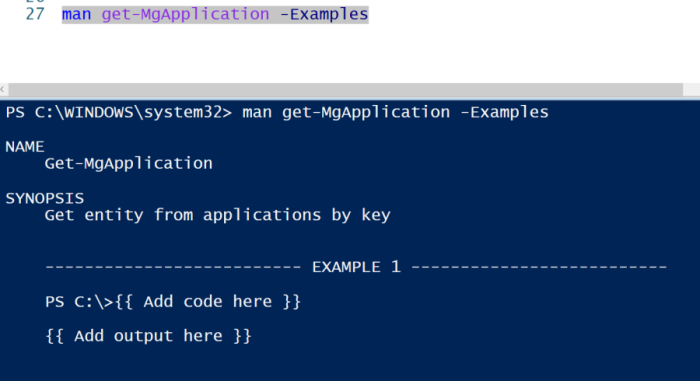
This uses the Microsoft.Graph module
Connect-MgGraph -AccessToken $token
$appToRotate = Get-MgApplication -Search "DisplayName:credRotateD" -ConsistencyLevel "eventual"
$pwCred=@{
"EndDateTime"=(Get-Date).AddDays(14) #default is 2y!
"displayName"="r345" #This sets the CustomKeyIdentifier, don't try to set it manually
}
$secret = Add-MgApplicationPassword -applicationId $appToRotate.Id -PasswordCredential $pwCred
Azure AD Graph
This uses the AzureAD module
Connect-AzureAD -TenantId $tenantId -AadAccessToken $AadAccessToken -AccountId $appId
$appToRotate = Get-AzureADApplication -SearchString "credRotateD"
$newSecret=New-AzureADApplicationPasswordCredential `
-ObjectId $appToRotate.ObjectId `
-EndDate (Get-Date).AddDays(14) `
-CustomKeyIdentifier "r345"